Key Takeaway
Many cyberattacks no longer look suspicious. Modern phishing emails often appear legitimate and are designed to trick employees into clicking links, opening attachments, or providing login credentials. For businesses and law firms, one mistaken click can lead to ransomware, data breaches, wire fraud, business interruption, and significant financial losses. Cyber liability insurance can help protect against these risks—but understanding your coverage before an incident occurs is critical.
Why Small Businesses and Law Firms Are Prime Targets for Cyberattacks
One of the biggest misconceptions about cybercrime is that hackers only target large corporations.
In reality, small businesses and law firms are targeted every day. According to Gartner research, end-user spending on information security is projected to reach approximately $215 billion globally in 2024, with financial institutions among the industries making the largest cybersecurity investments
Cybercriminals know that many smaller organizations can’t spend like financial institutions. They do not have dedicated cybersecurity teams or sophisticated security infrastructure in place.
They also know that employees are busy, moving quickly, and often handling large volumes of emails, invoices, contracts, and document requests throughout the day.
For law firms specifically, cybercriminals recognize the value of the information attorneys handle, including:
- Confidential client communications
- Financial records
- Settlement information
- Wire instructions
- Personally identifiable information
- Business and litigation documents
Because of this, law firms and professional service businesses have become increasingly attractive targets.
A Real Example of a Modern Phishing Email
Recently, I received a phishing email that looked legitimate at first glance.
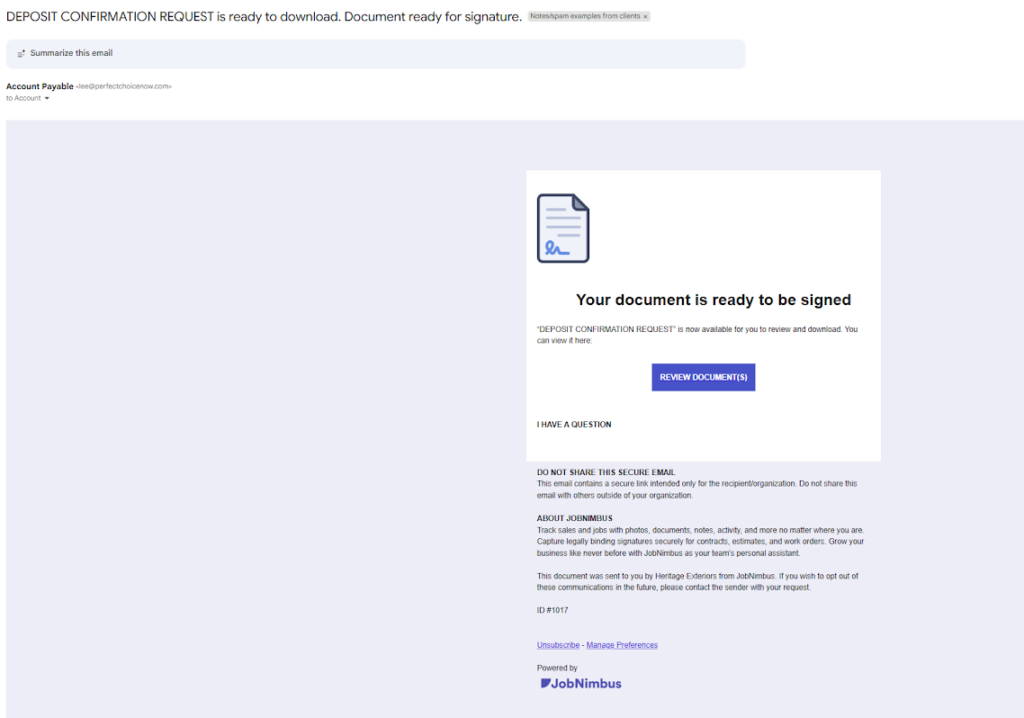
The subject line referenced a “Deposit Confirmation Request” and stated that documents were ready for signature. The email used professional formatting and branding that appeared to come from a legitimate business platform.
To someone moving quickly through emails during a normal workday, there would have been very little that immediately stood out as suspicious.
That is exactly what makes these attacks so dangerous today.
Years ago, phishing emails were often easier to identify because they contained obvious spelling errors, poor formatting, or unusual wording. Modern phishing attacks are much more sophisticated.
Many are carefully designed to resemble everyday business communications.
Common examples include:
- DocuSign requests
- Facebook account cancellations
- Deposit confirmation emails
- Shared document notifications
- Microsoft 365 login alerts
- Invoice requests
- Wire transfer confirmations
- Password reset requests
Cybercriminals understand that employees regularly interact with these types of emails, which increases the likelihood that someone will click without taking a closer look.
What Happens After Someone Clicks a Malicious Link?
Many cyber incidents begin with a simple mistake.
Once an employee clicks a malicious link or opens an infected attachment, several different things can happen depending on the nature of the attack.
Ransomware Attacks
One of the most common outcomes is ransomware. In these situations, hackers lock access to business systems and files until a ransom is paid.
This can bring normal business operations to a halt for days—or even weeks.
Data Breaches
A phishing attack may also allow cybercriminals to access sensitive client or customer information.
For law firms, this can create significant legal, ethical, and reputational concerns. It takes years to develop a stellar reputation and seconds to destroy it.
Wire Fraud and Financial Theft
Some attacks are designed specifically to compromise banking information or redirect wire transfers. Businesses handling real estate transactions, settlements, or vendor payments are particularly vulnerable. In the legal field, these attacks often target attorneys, paralegals, or office managers involved in client billing, wire transfers, or trust account administration.
Business Interruption
Even when data is recoverable, downtime itself can become extremely expensive. Businesses may lose revenue, productivity, and client trust while systems are being restored.
The Financial Impact of a Cyberattack
The costs associated with a cyber incident often extend far beyond repairing a computer system.
Businesses may face:
- IT forensic investigation costs
- Data recovery expenses
- Lost revenue from downtime
- Legal fees
- Breach notification costs
- Credit monitoring services
- Public relations expenses
- Regulatory penalties
- Increased insurance premiums after a claim
For many small businesses, even a relatively small cyber incident can create serious financial strain. According to industry research, the average cyberattack on a small or mid-sized business can cost over $250,000 once you factor in downtime, recovery costs, lost revenue, and other expenses.
Does General Business Insurance Cover Cyberattacks?
One of the most common misunderstandings I see is the assumption that standard business insurance automatically covers cyber-related incidents.
In many cases, it does not.
Some policies may provide very limited protection with small sub-limits, while others exclude cyber-related losses entirely.
That is why cyber liability insurance has become so important.
What Does Cyber Liability Insurance Typically Cover?
Coverage varies depending on the policy, but a properly structured cyber liability policy may help with expenses related to:
Forensic Investigations
Determining how the breach occurred and what systems or information were affected.
Data Recovery
Recovering or restoring compromised systems and files.
Business Interruption
Helping offset lost income during operational downtime.
Legal Expenses
Coverage for certain legal costs associated with a cyber incident.
Breach Notification Costs
Helping businesses comply with legal notification requirements after a data breach.
Ransomware and Extortion Expenses
Some policies may help cover ransomware-related costs depending on the circumstances and policy terms.
Because every business is different, it is important to review policy details carefully and understand what is and is not included.
Cyber Insurance Is Not a Substitute for Cybersecurity
Cyber liability insurance is an important part of risk management—but it should not replace good cybersecurity practices.
Businesses should still implement:
- Employee cybersecurity training
- Multi-factor authentication
- Strong password policies
- Email filtering and spam protection
- Regular software updates
- Reliable data backups
- Reputable IT support
Even with strong systems in place, however, human error remains one of the leading causes of cyber incidents.
And sometimes, all it takes is one click.
Final Thoughts: Review Your Cyber Coverage Before There’s a Problem
The reality is that no business is completely immune from cyber threats anymore.
Modern phishing emails are becoming increasingly convincing, and cybercriminals continue to target businesses of all sizes—including law firms and professional service providers.
Understanding your cyber risks—and your insurance coverage—before an incident occurs can make a significant difference in how disruptive and expensive a cyber event becomes.
If you are unsure whether your current policy adequately addresses cyber risks, it may be worth reviewing your coverage now rather than waiting until after a problem occurs.
